In the 2002 film Red Dragon, Francis Dolarhyde (Ralph Fiennes) is a serial killer who murders his victims as they sleep in their homes, at the behest of an alternate personality whom he calls the Great Red Dragon.
Dolarhyde proceeds to engage in necrophilic acts with the mothers’ corpses, while embedding shards of broken mirror glass into their eyes to watch himself.
FBI agent Will Graham (Edward Norton) deduces that Dolarhyde has very personal information about this victims – who they are, where they live, how many children they have, the layout of their homes, where to enter, and when best to attack. Dolarhyde knows this because he is a home video technician: he works for a lab that converts home video into VHS tapes. The hours of footage give him an intimate look into this victims’ lives.
He just had analog information. Imagine the damage if he had all the digital information about his victims.
Today, countless of Francis Dolarhydes have access to your private information, thanks to the Commission on Elections. And if you’re not outraged because you can’t visualize what 338 gigabytes of data are, maybe you can visualize what it can do:
Imagine someone opening a bank account under your name, using a fake driver’s license and passport. For years, your fake account is used to launder money, without your knowledge. Imagine your residential address easily accessed in one database. Imagine your email being targeted by phising scams. Or being the target of scams and extortion. Imagine a rogue politician using millions of voter data to keep track of his constituents in his municipality, creating detailed voter records and using this for political gain. All of this data is now out in the open.
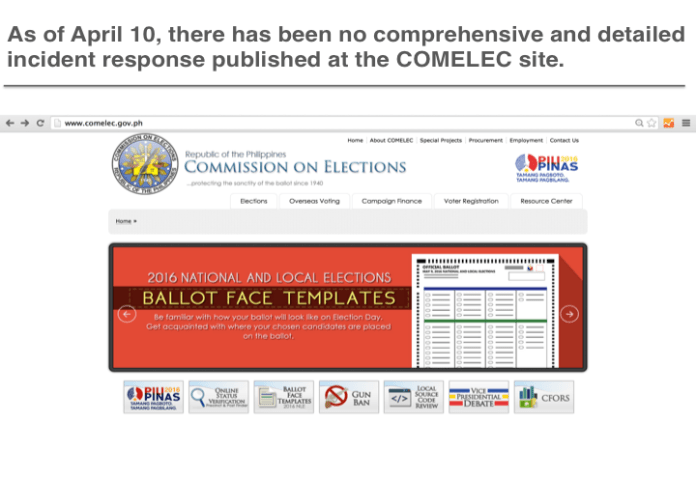
And the worst part? We don’t even know how exactly it happened or what steps are being done to make sure it doesn’t happen again. The COMELEC even downplayed it. Incredibly, COMELEC wasn’t event transparent enough to disclose what exactly what kind of data was leaked. Only Rappler did an in-depth report on what was actually in the data that was released.
The rest of local media has largely ignored this; it never made it to the headlines in the same way Kidapawan or the campaign trail did. It only received follow-up articles after Trend Micro, an IT security firm, released a blog post admonishing the government’s responses. None of the presidential candidates think this is a serious concern.
As a result, not only are we not seriously talking about it, most people don’t even know the breach happened. And there could be more breaches we don’t know about – according to security firm Mandiant, data breaches remains undiscovered for more than 6 months.
Make no mistake about it: the COMELEC breach is a disaster of national proportions: it’ll open the floodgates to more attacks and leave our institutions and economy vulnerable for years to come.
Gizmodo is now calling this one of the biggest government data breaches in history.
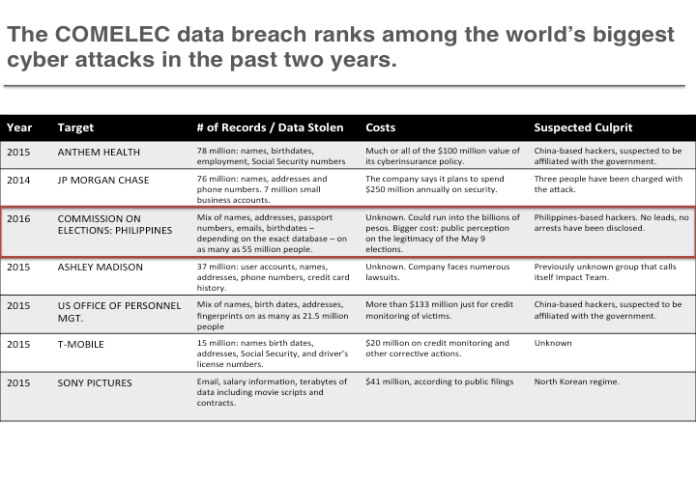
Sources: data compiled from Rappler.com, MIT Technology Review
The hackers posted the database online on March 27, more than two weeks ago. The fact that it is taking our collective brains so long to appreciate the gravity of this situation is a tragedy. It’s like a different parts of Philippine society got into a car pissed drunk, the driver falls asleep on/behind/in the wheel, and we are blissfully laughing (or arguing over which candidate performed best in the last debate) all the way to the car crash.

Dancing our way to the elections…
Why does this matter?
It matters because we have a $25 billion business process outsourcing industry that employs more than a million Filipinos. This industry survives on the trust of tens of thousands of corporate clients that their data would be handled securely.
It matters because the tension in the West Philippine Sea is leading to the most destabilizing geopolitical conflict of our generation. In this conflict, it’s been documented that one of our adversary’s potent weapons is cyber warfare and espionage. Can China bring the country to its knees by remotely shutting key telecommunications infrastructure, the internet, the electrical grid, and the water supply? Theoretically, it can. In this context, we should be grateful to Filipino hackers for pointing our vulnerabilities.
This conversation matters because the amount of data the government will capture about us will only grow exponentially in the next several years. By 2020, humanity will be producing 40 zettabytes of data. If that’s hard to imagine, picture this: if 1 gigabyte is equivalent to a cup of Starbucks coffee, 1 zettabyte is equivalent to enough Starbucks cups to fill the entire Great Wall of China.
And lastly, it matters because although the COMELEC’s automated election system is run as a separate network, the perception of legitimacy will be the most crucial outcome of a tight race like this (yes, Duterte Bros, it is still anyone’s bet). Didn’t a great rebel once say that “Revolution, as you know, is like gravity. All it takes is just a little push…“

Oh wait, I think he meant “madness”, not revolution. Just the same.
Why doesn’t COMELEC “get” the problem?
One clue is that none of the COMELEC commissioners has anything that remotely resembles a background in computer science, engineering, or data science. In an age of automated elections and biometric voter data, isn’t this very very strange?
Now, since our commissioners are esteemed legal luminaries, you might expect that they would have at least set in place the right institutional and legal framework to enable the COMELEC to protect its data. On this front, it seems there is more damning evidence.
For example, here’s the text of Republic Act 10367 – the law that requires mandatory biometric voter registration. Scroll down to Section 9 on database security and you’ll see this broadly articulated sentence: “The database generated by biometric registration shall be secured by the Commission and shall not be used, under any circumstance, for any purpose other than for electoral exercises.”
Now that sounds cool and sensible enough. After all, it’s not the job of the legislator to get into the practical, implemention-related details. That would fall under the jurisdiction of the COMELEC when it issues the Implementing Rules and Regulation for Republic Act 10367. It’s in the Implementing Rules and Regulations you would expect the COMELEC to at least spell out how it would provide for database security, who would be responsible, the milestones and steps involved, and the costs. Basis management stuff, right?
Here’s a copy of the IRR. Scroll to the relevant section on database security and you’ll notice the glaring fact that the IRR simply copied the text of the Republic Act. In short, there was neither a plan nor a framework from the COMELEC to secure it’s biometrics database (which according to Rappler, was part of the breach).
Another clue is the hard question on institutional checks and balances. As a separate constitutionally mandated commission, the COMELEC’s tech isn’t subject to the oversight of the DOST nor is its website part of the government’s web hosting service. As a result, nobody in its leadership team or its IT department are asking the right questions or providing a check and balance. This is admittedly a tough question to crack – how do you ensure the commission’s independence while ensuring that it’s tech adheres to global best practices? This is another case of technology development outpacing the ability of our laws to keep up.
Why has the media under-reported this story?
There are many obvious reasons for this. In an election cycle where journalists are spread out across the campaign trail and many more equally important stories coming up (Kidapawan, the RCBC-Bangladesh hearings, Poe’s disqualification, which candidate is which celebrity endorsing, etc), it’s easy for journalists and editors to fall into the trap of writing about stories where it is easy to get and verify primary sources (a campaign rally, a Senate hearing, a Supreme Court ruling, etc).
To understand the COMELEC data breach, journalists not only have to comb through the leaked data (which is exactly what Michael Bueza and Wayne Manuel did at Rappler), they have to get a crash course on database architecture, data warehousing, encryption, and network security.
Bring all of these together under an environment where news outlets prioritize speed, clicks, and eyeballs, and you’ll see the underreporting as a another case of market failure. And in every market failure, there’s an opportunity.
If you are a smart journalist, you’ll realize that the world is changing far faster than what seems to be apparent in your daily beats. You’ll realize that fundamentally, we are an island nation and an island people cut off from the world. And there are so many things out there that we don’t even know we don’t know.
You’ll realize that – due to no fault of your own – our educational system and current employers left us woefully unprepared for what is to come. And as a result, you’ll be taking steps to learn new stuff, from platform thinking to network effects.
You’ll be studying R, Python, and D3 on the side because this gives you a skill set that your peers (and editors!) won’t be able to match and makes you incredibly more valuable in the long run.
In Red Dragon, Will Graham had to break the rules to catch Francis Dolarhyde. He had to seek Hannibal Lecter’s counsel. He dug deep into the tragic pathology of his adversary. He had to stretch himself, learn completely new things, and find his own Great Red Dragon.